In this guide, you will learn how to check a file hash value using PowerShell.
This will work on any file type, exe, msi, docx, pdf, iso, and so on.
A file hash is a unique value that corresponds to the content of the file.
Checking a file hash value is often used when downloading files from the internet and you want to verify the integrity of the file (it has not been modified). Some websites will post the hash value of the file and after downloading it you can check the hash value to verify it matches.
If the hash is different, then the file has been modified or is corrupt.
How to Check File Hash?
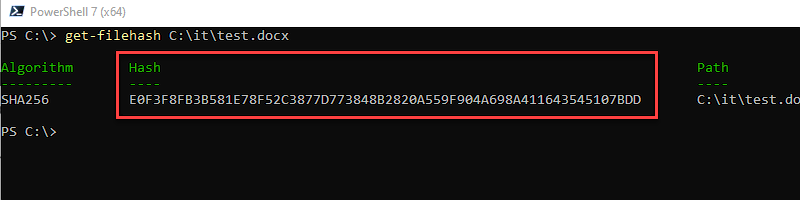
You can check the hash value for a file by using the PowerShell command get-filehash and the path to the file. In the example below, I’m getting the hash value for a file called test.docx on my local computer. By default, this command used the SHA256 algorithm.
get-filehash c:\it\test.docs
Here is a screenshot from my local computer.
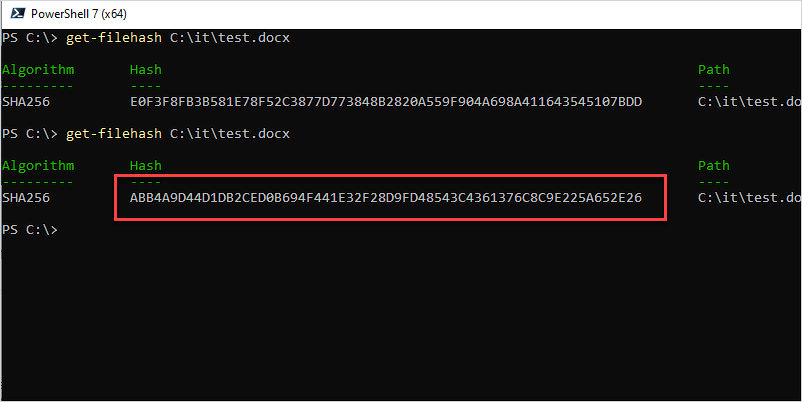
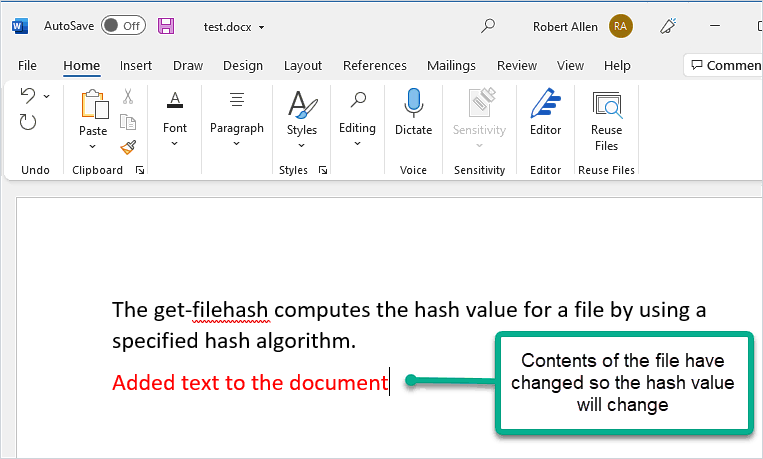
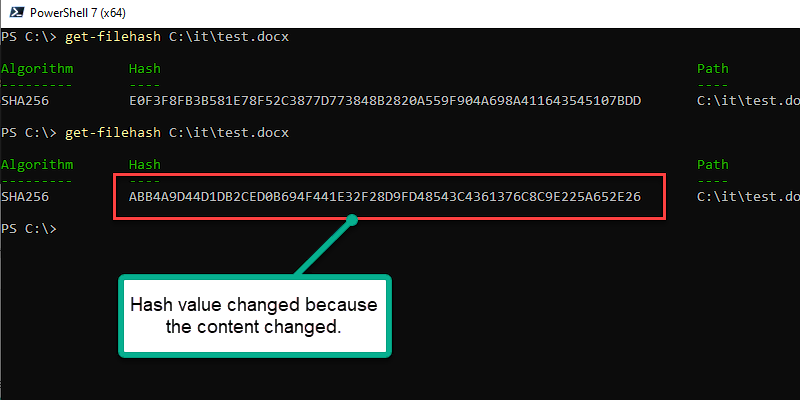
The hash is based on the contents of the file. If the contents of the file change, then the hash will change. I’ll demonstrate this by opening the document and adding the words “added text to document”.
Now if I run the get-filehash command again you will see that the hash value has changed.
If you rename the file or change the file extension the hash value will not change, again this is because the hash is calculated based on the contents of the file, not the filename or extension.
What is the Importance of a Hash Value?
You now know how to check the hash value but how does this help you? Software developers sometimes list the hash value of a file on their website, this will help you verify the file’s integrity.
The purpose of publishing the hash is so you know the file you are downloading is from the developer and has not been modified.
I’ll walk you through a real-world example.
On my website, I offer a free trial download and post the hash value of the file.
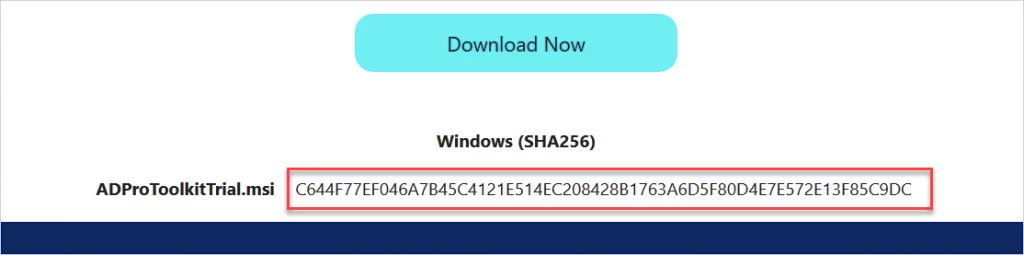
After downloading you can run the get-filehash command on the msi file to check its integrity. (make sure it has not been altered).
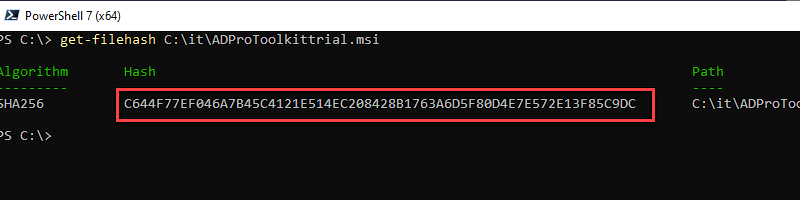
You can see in the above screenshot the downloaded file has the same hash value as displayed on my website. This lets you know the contents of the file have not been modified. If a hacker had injected code into the file, then the hash value would have changed and would not match what I posted on my website.
Hash values are also used in various security products like firewalls, IDS, endpoint protection software, and so on. If one of these programs detects a file is malicious, then it can be blocked based on the hash of the file. This is important because the file could be named after a legitimate windows file like cmd.exe or svchost.exe. These are actual file names of real programs on a Windows computer.
But the malicious file would have a different hash value from the legitimate file on a computer, this would allow you to block the malicious file based on the hash.