Active Directory contains five roles called Flexible Single Master Operation Roles (FSMO), these roles are required for the domain controllers to function correctly. During the first domain controller installation, the FSMO roles are installed automatically. In most cases, they can be left alone, but there are times when they need to be moved such as a failed DC.
It is a good idea to be familiar with where the roles are installed in your AD environment, you never know when a disaster will hit. In this post, I will walk through two simple methods on how to list fsmo roles. The first method uses the Netdom query command and the second uses Windows PowerShell.
There are two forest wide roles and three domain wide roles
Forest Wide Roles:
- Schema Master
- Domain naming master
Domain Wide Roles:
- PDC
- RID pool manager
- Infrastructure master
Now let’s take a look at how to query the FSMO roles.
Method 1: Netdom query fsmo command line tool
Netdom is a command line tool used to manage Active Directory domains and trusts. The Netdom tool is built into Windows Server 2003 and up.
1. On any domain controller open the command prompt. On Windows 2012 server click the start button and type cmd, windows will search and return the command prompt. Click on “Command Prompt”.
2. From the command prompt type “netdom query fsmo” and hit “enter”.
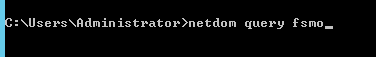
The above command should return the five roles and which DC they are on.
That’s it for the Netdom query method, very simple and straightforward.
Method 2: Powershell Get FSMO Roles
Using Powershell will require two lines of code, one to return the forest roles and another to return the domain roles.
1. Open windows Powershell. On 2012 server click start and type Powershell. Click Windows Powershell from the search results
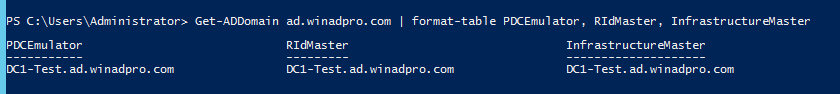
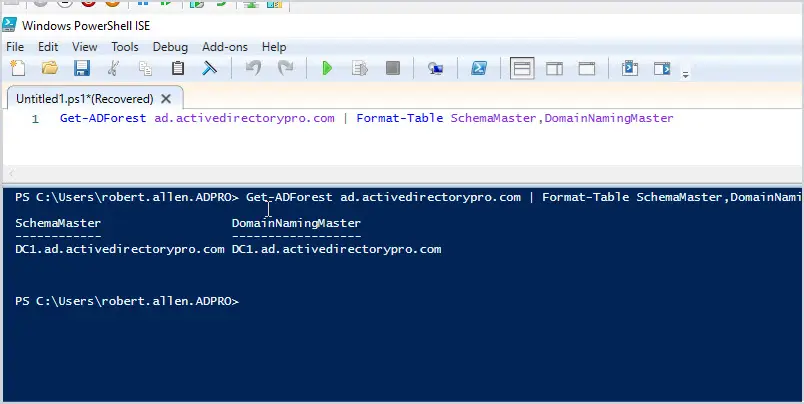
2. From the PowerShell command line type: Get-ADForest yourdomain | Format-Table SchemaMaster,DomainNamingMaster
The above command returns the forest FSMO roles.
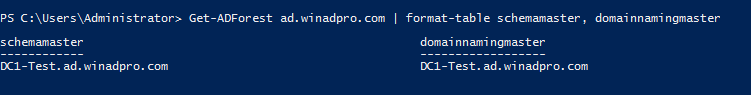
3. Type: Get-ADDomain yourdomain | format-table PDCEmulator,RIDMaster,InfrastructureMaster
The above command will return the domain FSMO roles.
That’s it for method two.
I recommend becoming familiar with which DCs in your environment hold the FSMO roles. It’s good to understand what these roles are and the DCs that hold them in case a disaster does occur or you have a specific reason to move them.
Awesome Thanks!
I use a different method every time to keep myself fresh. Last time I intentionally used the GUI for Active Directory Schema, Site and Services and Users and Computer to migrate all the five FMSO roles but I agree that the command line and PowerShell options are preferable.
Very useful, thanks!
No problem!
this is very useful thanks
very useful. Thanks
Thanks, that was so much easier!